OLD Times
There are rumors that a group of people would like to overthrow the communist party. Therefore, an investigation was initiated under the leadership of Vlaicu Petronel. Be part of this ultra secret investigation, help the militia discover all secret locations and you will be rewarded.
Googling for Vlaicu Petronel brings us to https://twitter.com/PetronelVlaicu.
There are no hints here, but more information can be found on the Wayback Machine:
- https://web.archive.org/web/20191206221532/https://twitter.com/PetronelVlaicu/
- https://web.archive.org/web/20191207122830/https:/twitter.com/PetronelVlaicu/
First link shows 1XhgPI0jpK8TjSMmSQ0z5Ozcu7EIIWhlXYQECJ7hFa20 as hint, second one has the text I love Google G Suite services!.
Trying the id on Google Docs brings us to a document that has the text:
The local activity is under control. People seek their daily routine and have no doubts about the party, except for one man: Iovescu Marian - who goes by the name of E4gl3OfFr3ed0m
Github
We can find the username E4gl3OfFr3ed0m on Github with a repository called resistance.
Inspecting the Git history with tig we can see a commit message called top secret that commits a .php script:
<?php
$myfile = fopen("locations.txt", "r") or die("Unable to open file!");
$locs = fread($myfile,filesize("locations.txt"));
fclose($myfile);
$locs = explode("\n",$locs);
$reg = $_GET["region"];
if($reg < 129 && $reg >= 0){
echo "<b>[".$reg."]:</b> ";
echo $locs[$reg];
}
else{
echo "<b>Intruder!</b>";
}
?>
In another commit, there is a reference to an URL: http://138.68.67.161:55555/.
Locations
The locations can be retreived via http://138.68.67.161:55555/spread_locations.php?region=1 [1-129]
Obtaining all locations will result in the following (truncated) output:
<b>[0]:</b> 22.5277957,47.3561089
<b>[1]:</b> 22.5497683,47.184652
<b>[2]:</b> 22.5277957,47.0276192
<b>[3]:</b> 22.538782,46.8851427
<b>[4]:</b> 22.5607546,46.6669469
<b>[5]:</b> 22.5827273,46.508391
<b>[6]:</b> 22.7365359,47.0051481
<b>[7]:</b> 22.9342898,47.0500808
<b>[8]:</b> 23.14303,47.0425947
<b>[9]:</b> 23.2968386,47.4527737
[...]
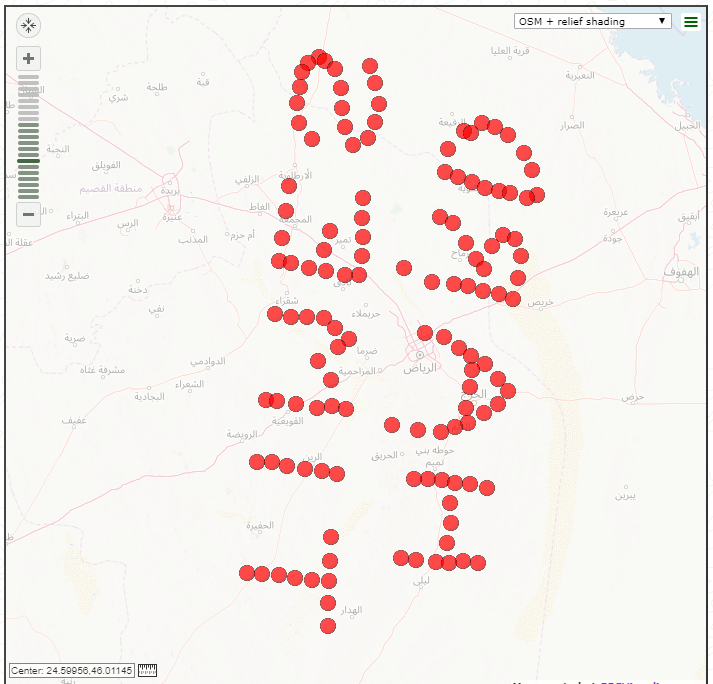
GPS
Data plotted on map via https://www.gpsvisualizer.com/:
Flag
HackTM{HARDTIMES}